With a renewed focus on building better relationships between police and their communities, 21st century policing has led law enforcement agencies across the country to reevaluate how they operate. Establishing law enforcement's role in community safety is not easy while managing changing expectations of transparency, critical staffing shortages, and rapid technological advancements.
As your department rises to meet these challenges, your key control practices should evolve accordingly. Start by remembering these three T’s: transparency, turnover, and technology.
Transparency
As the public’s perception of policing changes, transparency builds trust with your community. However, it’s important for your behind-the-scenes processes to support your culture of transparency and accountability.
It’s important for your behind-the-scenes processes to support your culture of transparency and accountability.
For example, a department might demonstrate its commitment to transparency by publishing its policies and practices. But process breakdowns that don’t align with those principles and best practices will damage the public’s trust in the department. Consider these scenarios:
Scenario 1
|
Scenario 2
|
Complete transparency and accountability require a comprehensive approach that spans from high-level policies to daily operations. To that end, maintaining an audit trail of how staff use keys, radios, weapons, and other equipment helps ensure officers are using keys and other assets appropriately. If any incidents occur, you’ll have documentation to help with investigating the issue.
Turnover
Law enforcement staffing has reached critically low — even dangerous — levels across the nation. According to the Police Executive Research Forum, agencies face a triple threat of fewer applicants, more resignations, and looming retirements.
.png?width=770&height=322&name=KT%20Stats%20(7).png)
Considering these challenges, it's crucial to implement a key control process that can withstand personnel changes, using the following guidelines.
Clearly Document Key Control Policies
Having written procedures helps new employees understand expectations and ensures consistency in key control practices. Regularly review and update your policies and practices to adapt to changing needs and challenges.
Reduce Manual Steps
Traditional key management processes that heavily rely on a key control officer and physical logbook are time-consuming and prone to errors, especially during personnel transitions. Digitize your key control process to give staff an efficient way to check keys in or out, reducing the paperwork and administrative burden tied to manual key logs.
Promptly Revoke Key Access When Employees Leave
To avoid unauthorized access, develop protocols for promptly collecting keys when employees leave or change roles. Be sure to disable any fobs, access codes, or key control system user accounts. Regularly run reports of active user accounts and currently checked-out keys to make sure no keys fall through the cracks.
Provide Regular Key Control Training
Keeping personnel informed about best practices and process updates helps maintain secure, effective operations.
With a streamlined key control process, personnel will be able to focus on their core duties, even as people come and go.
Technology
In the 21st century, technology has become integral to everyone’s lives. That means more crimes are committed online and more aspects of law enforcement involve advanced equipment, so today’s police officers must be comfortable with technology.
As younger, tech-savvy officers join the force, they expect seamless technology and are quick to leave roles that rely on outdated, inefficient processes. As such, they might be frustrated with manual processes like filling out key logs.
As younger, tech-savvy officers join the force, they expect seamless technology and are quick to leave roles that rely on outdated, inefficient processes.
Using electronic key control instead of outdated manual processes saves time, reduces errors, and prevents significant disruptions. When implementing a key control solution, take advantage of the following capabilities.
Automate the Key Audit Trail
By automatically authenticating employees and recording who removes a key, when, and why, you’ll reduce the administrative burden of the key control process.
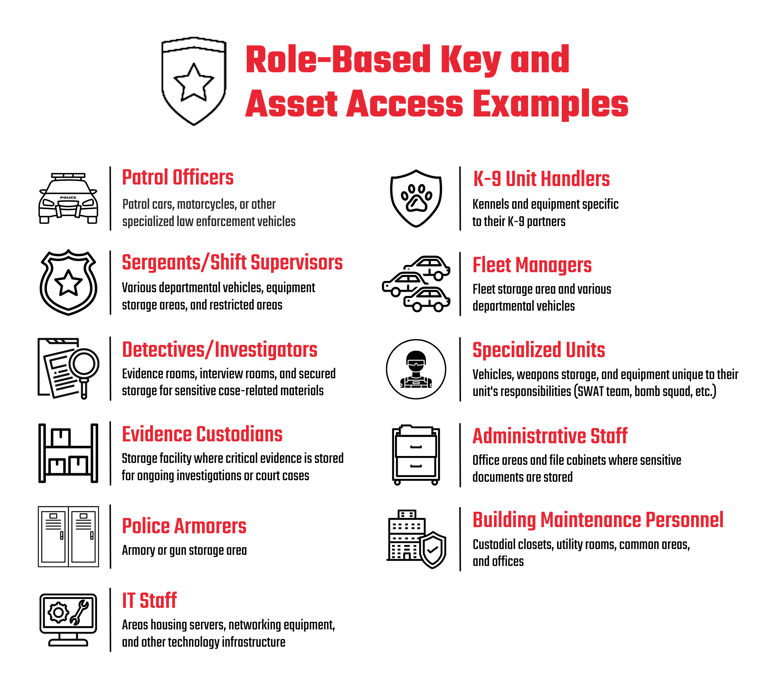
Set Up Role-Based Key Access
Electronic key control systems can restrict access to specific keys based on specific job responsibilities to reduce the risk of unauthorized use or theft.
Enable Automatic Reporting and Notifications
To help you respond quickly to potential issues, key control systems can send automated reports to key control officers or command staff. If a key is overdue or has been accessed outside of a designated time frame, the system can send a text or email alert.
Run Efficient Key Audits
Frequent key audits help you ensure all keys are accounted for and properly documented. Electronic key control systems allow you to quickly run key control reports, saving you hours of sorting through manual records and counting keys.
Manage Small Equipment Along With Keys
If your key control system has the option for electronic locker modules, you can secure small items such as mobile devices, radios, or weapons, along with your keys. Just as you do with keys, set up access levels for each locker to ensure only authorized personnel are able to access assets.
With technology shaping modern policing, it’s important to embrace digital solutions for managing keys. By doing so, you can support tech-savvy officers in their roles, streamline operations, and enhance security.
In the modern era of law enforcement, an effective key control policy meets the demands of transparency, turnover, and technology. By empowering your personnel with streamlined processes, embracing technology, and upholding unwavering transparency, you’ll be well equipped to serve and protect your community.