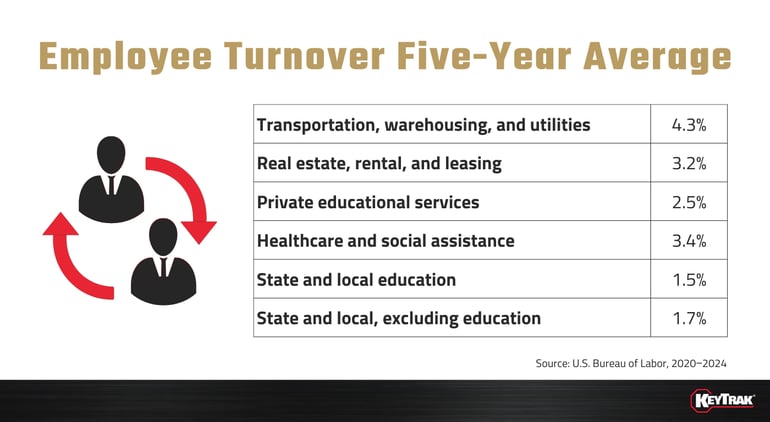
Organizations in every industry have something in common: employee turnover. From 2020 to 2024, the five-year average annual turnover rate nationwide was just under 4%. While that might seem low, in July 2025 alone, there were nearly 5.8 million total separations!
 NOTE: Annual average total separations rates are calculated by dividing the sum of the U.S. Bureau of Labor Statistic's monthly separations levels by the sum of monthly employment levels, and multiplying that quotient by 100.
NOTE: Annual average total separations rates are calculated by dividing the sum of the U.S. Bureau of Labor Statistic's monthly separations levels by the sum of monthly employment levels, and multiplying that quotient by 100. Turnover's effect on your organization is more serious than you may realize. In addition to being expensive, attrition can also create holes in your organization’s key management practices. Here are the three main ways that turnover will sabotage your key control.
When employees who had access to keys leave the company, failing to revoke access privileges and collect all keys in their possession immediately after they leave is a major risk to your facility. Consider the potential consequences of not having the necessary tools or policies to collect keys from staff members who have parted ways with your organization. How much damage could a former employee inflict with a key or two? What areas of your facility would they be able to enter? What sensitive assets would they have access to?
An electronic key control system would be able to deter ex-employees from stealing your keys, thanks to features like biometric logins and a secure drawer that can only authorized users can open. When an employee leaves, return any keys in an employee’s possession to the key control system and revoke their user access privileges.
Another potential problem that turnover causes for key control is when your key control officer/administrator or other experienced employees leave your organization, taking valuable knowledge with them.
Whether an employee had valuable experience and detailed knowledge of key security policies, losing them hurts. But you can do multiple things to help overcome the loss.
One of these things is to document all key control policies, which helps new employees you bring in as replacements (more on that later). To encourage employees to follow your policies, you can use an electronic key control system to help enforce your key management protocol. You could start by assigning user access levels for each employee. That way, anyone without access for certain keys won’t be able to sign them out — or steal them.
One final way to ensure you aren’t left out to dry when experienced employees leave is to assign more than one person to be in charge of key control. If possible, you should look at people with more than one year at your company and who are familiar with how things are run.
When you experience turnover and replace the old employees with new ones, the new staff members lack the knowledge about the way your company runs and won’t be familiar with every policy right away. This lack of knowledge may cause them to make mistakes or be slow with decision making. Once again, this is a great example of why you should document all policies and ensure employees are familiar with them.
If you do have an electronic key control system in place already, new employees may experience a learning curve as they familiarize themselves with how your business uses the system. To make this process as smooth as possible, offer training in multiple formats to appeal to different learning styles.
Experienced employees leaving and inexperienced ones coming in make the job of protecting keys a little more difficult, but it doesn’t have to be so hard. If you take the necessary precautions, you can stay on top of the key control game. Just because your employees are leaving doesn’t mean your key control has to go with them.
Former Employees Retain Key Access
When employees who had access to keys leave the company, failing to revoke access privileges and collect all keys in their possession immediately after they leave is a major risk to your facility. Consider the potential consequences of not having the necessary tools or policies to collect keys from staff members who have parted ways with your organization. How much damage could a former employee inflict with a key or two? What areas of your facility would they be able to enter? What sensitive assets would they have access to?
An electronic key control system would be able to deter ex-employees from stealing your keys, thanks to features like biometric logins and a secure drawer that can only authorized users can open. When an employee leaves, return any keys in an employee’s possession to the key control system and revoke their user access privileges.
Experienced Employees Take Their Knowledge With Them
Another potential problem that turnover causes for key control is when your key control officer/administrator or other experienced employees leave your organization, taking valuable knowledge with them.
Whether an employee had valuable experience and detailed knowledge of key security policies, losing them hurts. But you can do multiple things to help overcome the loss.
One of these things is to document all key control policies, which helps new employees you bring in as replacements (more on that later). To encourage employees to follow your policies, you can use an electronic key control system to help enforce your key management protocol. You could start by assigning user access levels for each employee. That way, anyone without access for certain keys won’t be able to sign them out — or steal them.
One final way to ensure you aren’t left out to dry when experienced employees leave is to assign more than one person to be in charge of key control. If possible, you should look at people with more than one year at your company and who are familiar with how things are run.
New Employees Aren’t Up to Speed
When you experience turnover and replace the old employees with new ones, the new staff members lack the knowledge about the way your company runs and won’t be familiar with every policy right away. This lack of knowledge may cause them to make mistakes or be slow with decision making. Once again, this is a great example of why you should document all policies and ensure employees are familiar with them.
If you do have an electronic key control system in place already, new employees may experience a learning curve as they familiarize themselves with how your business uses the system. To make this process as smooth as possible, offer training in multiple formats to appeal to different learning styles.
Experienced employees leaving and inexperienced ones coming in make the job of protecting keys a little more difficult, but it doesn’t have to be so hard. If you take the necessary precautions, you can stay on top of the key control game. Just because your employees are leaving doesn’t mean your key control has to go with them.
This post was originally published in 2019 and updated in 2025.

![Employee Resignation Concept [849574890] copy Employee Resignation Concept [849574890] copy](https://blog.keytrak.com/hs-fs/hubfs/Employee%20Resignation%20Concept%20%5B849574890%5D%20copy.jpg?width=3000&height=606&name=Employee%20Resignation%20Concept%20%5B849574890%5D%20copy.jpg)
