In 2024, 91% of respondents said physical security incidents increased or stayed the same, up from 87% the previous year. Rising local crime (23%) and the economy (15%) were the most common reasons cited, along with insider problems, security guard shortages, supply chain disruptions, and reduced business hours.
In fact, these factors are all employee theft risks, representing motivation (financial pressures), means (physical access), and opportunity (lack of supervision). Implementing key management systems is a critical step in reducing theft risks by controlling who can use keys and assets. But how do you know if employees are abusing their access?
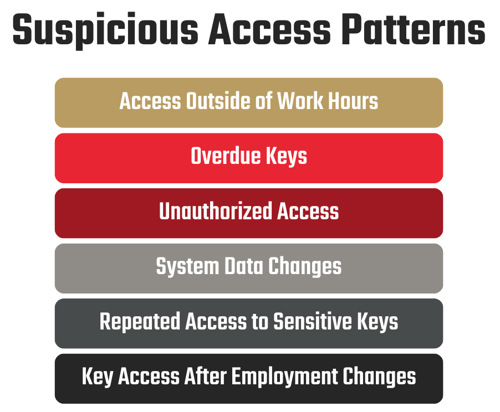
To detect potential security incidents, watch for unusual key activity. Let’s look at some of the most common suspicious access patterns.
Access Outside of Work Hours
If an employee is frequently checking out keys outside their normal working hours, that could indicate they’re using assets for reasons unrelated to their jobs. To prevent these situations, set up time-based limitations on your key control system so employees can’t check out keys after hours.
Example Scenarios
- A customer service agent checks out a fleet vehicle after their shift. Since they don’t have any planned work responsibilities requiring transportation, it’s possible they’re using company vehicles for personal reasons.
- A project manager schedules time off during the holidays. However, the key log shows that they checked out a key to a storage room containing sensitive files during their time off. This type of activity might suggest they’re retrieving information for illicit reasons.
Overdue Keys
If an employee doesn’t return keys on time, it could mean they simply forgot, but it could also point to lost keys or a breach in security protocols. Be sure to set up alerts on your key control system to notify you of overdue keys so you can promptly follow up with the employee who has the key checked out.
Example Scenarios
- A network engineer completes a project and fails to return the data center key by the end of the day. Having the key to such a high-security area checked out for longer than necessary increases security vulnerabilities.
- A truck driver fails to return a fleet key at the end of their scheduled shift, which should prompt further inquiry into the reason for the delay to ensure company assets are appropriately managed.
Unauthorized Access
Look for system activity that indicates unauthorized key use, such as leaving the system unattended after opening a drawer or panel or someone taking more keys than they requested. An electronic key control system flags and records such instances so you can address attempted breaches.
When checking for unauthorized access, an important thing to note is how your system logs key removal. If it requires employees to scan key tags, for example, it’ll be more difficult to detect when someone removes more than one key. On the other hand, if your system automatically logs a key’s removal the moment it’s pulled, you’ll be able to quickly detect when someone removes an unauthorized key.
| TIP: If you have a KeyTrak system, run the Alarm Activity, Drawer Activity, Tag Activity, and Idle Activity reports. If you’re a KeyTrak Guardian user, check the Security Camera report as well. |
Example Scenarios
- A facilities manager requests a storage room key and leaves the key control system’s drawer open for longer than necessary without removing the requested key. This action could allow someone to remove a key without authorization while the drawer is open.
- A warehouse supervisor checks out a forklift key, which is within their access level. While removing the key from the system, they also take a research and development lab key, which they’re not authorized to have. Removing the unauthorized key could indicate the employee is trying to discover trade secrets.
System Data Changes
If someone frequently alters system data (e.g., changing key tag names, adding users, or editing checkout reasons), that could be a sign of someone trying to conceal their behavior. However, it’s important to consider the context to determine if the changes are legitimate. To reduce this risk, limit the number of users who have administrative rights.
| TIP: If you have a KeyTrak Edge system, run the Audit Trail report to see a log of all system changes, who made them, and when. |
Example Scenarios
- A system administrator adds multiple users and key tags within a single week. For admins, this type of activity isn’t unusual unless it’s accompanied by other behavioral red flags.
- An administrative assistant changes the name of a key tag from “Data Center” to “Supplies Storage Room,” which suggests they’re attempting to disguise unauthorized key access as a legitimate need.
Repeated Access to Sensitive Keys
Someone repeatedly checking out high-security keys can raise concerns if an employee doesn’t have a legitimate need to enter certain areas or if their key activity doesn’t align with their job responsibilities.
To prevent unauthorized removal of sensitive keys, set up alerts on your key control system to notify you when an unauthorized user has taken a high-security key or hasn’t returned it on time. In addition, set up user profiles that ensure employees only have permission to check out keys critical to their job roles.
Example Scenarios
- An accountant removes a data center key despite their job responsibilities not requiring access to the data center.
- A custodian checks out a key to an executive’s office four times in a week even though they’re only required to clean the space three times a week.
Key Access After Employment Changes
Allowing an employee to retain access to keys after an employment change, such as a termination or an internal transfer, increases your risk of insider threats. To prevent unauthorized key use, update a user's system privileges if they change roles within your business. When employees leave your organization, immediately collect all the keys they have and revoke their user privileges in your electronic key control, access control, and software systems.
To ensure no one slips through the cracks, review the users listed on your key control reports to ensure they’re all current employees and have key access appropriate for their job responsibilities.
Example Scenarios
- An IT support technician transfers to the human resources department. They occasionally check out a key to the equipment room, which is within the user's access level to due to their previous role. However, the employee’s current responsibilities don’t involve that room.
- A terminated controller returns to the business and follows an employee inside. Using a key they failed to return, they enter their former office and remove confidential files.
By recognizing unusual key access patterns, you’re taking a proactive approach to protecting your business against insider threats and theft. Electronic key control systems give you the means to not only monitor irregularities but respond quickly to physical security incidents. You might not be able to control the economy and other risk factors that give employees a motive to steal, but planning your response can limit the means and opportunity.


