From unauthorized access to compliance violations, poor key control can undermine both safeguards and daily operations. The best defense is a proactive strategy. Regular key audits strengthen security, ensure compliance with industry standards, and boost accountability across your team.
Whether you’re managing a small facility or a multi-site operation, following the below key audit best practices helps your organization stay secure and running smoothly.
Why Key Audits Matter
A key control audit is a full review of your organization’s keys: what keys exist, who has access, and how they’re being used. They allow you to:
Control Key Access
Audits help identify missing keys or outdated access permissions. Regular reviews allow you to catch and correct these vulnerabilities before they escalate to theft or misuse.
Meet Compliance Requirements
Many industry standards and regulatory requirements mandate strict control over physical access. Examples of these standards include:
-
HIPAA mandates protection for areas containing sensitive health data.
-
ISO 27001 requires tracking access to facilities.
-
PCI DSS requires proper handling and return of keys.
Failing to meet these requirements can result in fines, penalties, or reputational damage.
Protect High-Value Assets
From equipment and inventory to sensitive data and restricted areas, key audits ensure only authorized personnel can access critical assets.
Improve Accountability and Efficiency
When employees know keys are tracked and regularly reviewed, accountability naturally improves. Audits also help eliminate redundant or outdated keys, reducing confusion.
When to Perform Key Control Audits
There’s no one-size-fits-all schedule for audits, but here are several scenarios where it’s important to review your key activity:
-
On a Scheduled Basis: Conduct audits monthly, quarterly, or annually, depending on your organization’s size and risk level. Many businesses align audits with fiscal end-of-year reviews or operational cycles.
-
During Personnel Changes: Any time an employee leaves, transfers, or changes roles, review their key access immediately.
-
After Security Incidents: Lost keys, theft, or unusual key activity should always trigger an audit, as these incidents often reveal security gaps.
-
Following System or Process Updates: Changes like new locks, updated procedures, or software implementations can create inconsistencies in your key management process.
-
Ahead of Financial or Compliance Audits: Reviewing your key activity before a formal third-party audit helps avoid surprises.
-
On an Ad-Hoc Basis: Sometimes leadership may request an audit to validate processes, investigate concerns, or proactively reduce risk.
Regular key audits will help protect your business from loss, theft, and security violations year-round.
Steps to Conduct an Effective Key Audit
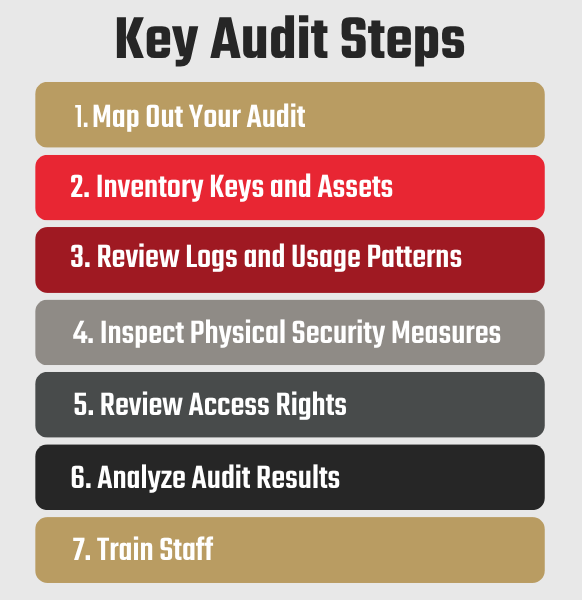
Not sure where to start? Follow these steps for a thorough, successful audit:
1. Map Out Your Audit
Start by defining your objectives, scope, and frequency. Are you auditing all keys or focusing on high-risk areas? Clear goals keep the process efficient.
2. Inventory Keys and Assets
Create or update a complete list of keys, including who they’re assigned to and what they access. Be sure to account for spare keys.
3. Review Logs and Usage Patterns
Look for discrepancies such as unreturned keys, unusual usage, or gaps in tracking. These can signal potential issues.
4. Inspect Physical Security Measures
Check locks, storage systems, and access points. Reinforce your physical security measures by storing keys securely in an electronic key control system that’s only accessible to authorized individuals.
5. Review Access Rights
Remove or reassign keys as needed. Immediately revoke access for former employees or outdated roles.
6. Analyze Audit Results
A key audit reveals how effectively your key control policies and procedures are working in real-world conditions. Look for issues such as:
-
Discrepancies between system records and actual key assignments
-
Missing or unreturned keys
-
Access permissions that aren’t aligned with current roles and responsibilities
-
Recurring usage patterns or process breakdowns
-
Outdated or incomplete records
Once you’ve reviewed the results, use these insights for targeted policy updates and training.
7. Train Staff
Clearly communicate expectations and train employees on key control best practices. Your team should understand their responsibilities when it comes to key usage, storage, and return.
Simplify Your Audits
Electronic key management systems simplify audits by providing verifiable tracking, automated alerts, and detailed audit trails. These tools reduce manual errors and improve overall visibility.
Key control audits are one of the best ways to strengthen your organization’s security posture. They help prevent unauthorized access, support compliance with industry standards, and improve operational efficiency, all while reinforcing accountability across your team.
By making audits a regular part of your operations rather than a reactive measure, you can reduce security risks, support compliance, and improve operational efficiency, all while reinforcing accountability across your team.


